3 phishy things to watch out for
The key to protecting yourself from phishing attacks and email scams is to recognize the elements used to trap you.
Phishing is the use of social engineering on the Internet that tries to get you to click on links or enter your personal credentials like passwords, bank or credit card details, or other personal data. Basically, it’s bad guys trying to trick or con you to give them your confidential information.
In my tutorial last week, I covered the 3 Keys to Protect Yourself From Phishing Attacks. I shared the secrets to help you get in the right mindset the next time you receive a suspicious email. After reading part one of this series on phishing:
- You know that email is not a real-time communication tool, so you don’t have to rush to click on any of the links. You can take your time to convince yourself this is a legitimate email from your bank.
- You know that major organizations don’t make mistakes in the material they send to their customers. You haven’t noticed any branding mistakes or typos in the text, and so you’re ready to move on to the next step.
- You know that your bank wants to hear from you when it comes to security. If anything about the email doesn’t look right to you, you won’t hesitate to call them instead of clicking on any of the links.
If you keep the above in mind, you’ll be in great shape to not get caught on the hooks that are used in phishing emails to catch unsuspecting people.
Now, let’s take a look at a couple of actual of phishing examples that the bad guys use to snare people.
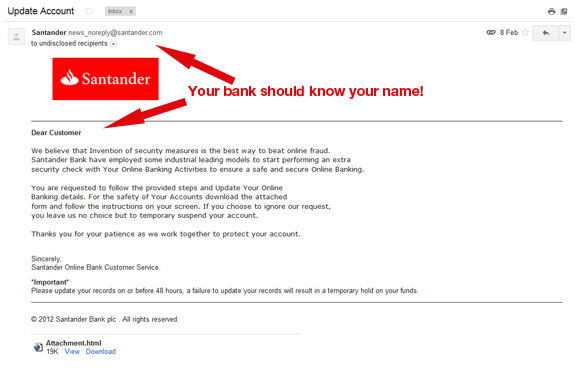
First things first, there was nothing in the sender or subject lines to tip you off that this was a phishing scam, so you clicked on the email from your bank or corporation – well, at least it looks like it’s from a legitimate corporation.
Various and sundry email addresses.
One of the telltale signs of a phishing attack is when your bank doesn't know your name! When you receive an email addressed to undisclosed recipients or unknown, yet it demands action in order for your account to not be closed, then something is wrong.
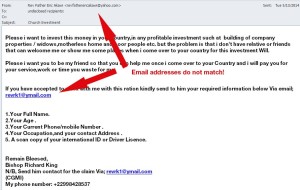
Another sign of phishing attacks is that they often include multiple email addresses with different domains within a single email. Take a close look at the domains of the email addresses and you’ll notice that they often don’t match that of the organization they claim to be from. That’s a sure give-away that something phishy is going on.
For example, emails from Target will be sent from the target.com domain and not from target.bfio.com.
Another thing you’ll see that should set the alarm bells off in your head is the use of free email addresses in emails that are supposedly from major corporations.
You can be sure that correspondence from a major company will NEVER include a yahoo.com, Hotmail.com or other free email service.
Links. Links. Links.
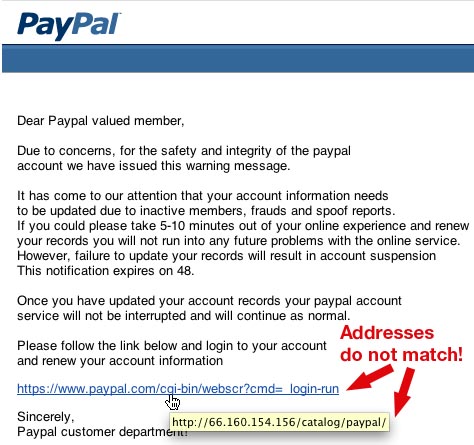
We’ve all grown so used to clicking on links on websites and emails, that it’s pretty easy for the bad guys to take advantage of our trust. Most people instinctively click on links because they expect that the link will take them to a continuation of what they were reading, pertinent information, or some other desirable website.
Just like false or fake emails used in phishing attacks, the bad guys use links to mislead you. They’ll mask the links a bit in order to conceal their malicious intent, but it takes only a little effort to expose most fake links.
- Links that look like they go to the real web site, but don't. Lots of times, you'll see a link in the text that looks legitimate, but when you hover your mouse over it - without clicking! - and check the real address, you'll see that they are sending you to a different address. If you see any difference between the link in the text of the email and the url when you hover over it, then don't click on it.
- Links that begin with an IP addresses. Most major companies don't use IP addresses in their links.
- Links that download executable files to your computer. It would be unusual for a major company to send you a file in this way.
- Legitimate companies will use secure HTTPS connections when requesting any personal information. If you don't see HTTPS, then you should be suspicious.
Make sure to check the links.
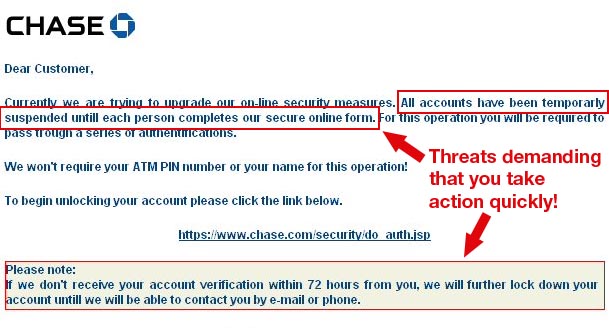
Threats
Don’t be intimidated by threats that are part of almost all phishing attempts. The bad guys use threats to make you nervous and uncomfortable to get you to click on one of the links that is actually a trap. They need you to feel under pressure to act now. Typical threats include:
Your service could be suspended!
Your online account is locked
Helpdesk – Urgent Notification!
Your Account has been Terminated
Whenever you receive an email threat or demand for you to act immediately in order to keep your account active, or to stop some action against you – STOP before you click on anything.
Call the number on their website. If this really is a legitimate notice from your bank, then it’s likely that talking with someone on the phone is the best way to clear up a problem that involves your account being closed.
If it’s not legitimate, then calling the bank can save you money and even your identity.
The main thing is that if at any point, you have any doubts about the veracity of the email, then call the bank or company that is claiming to have sent the email.
When it comes to security, your bank wants to hear from you!
If you suspect something is a phishing attack, then check out snopes.com. It’s one of my favorite resources for checking if something is a known Phishing scam.
How can we improve the answer?
Send feedbackThank you!
Thank you! We will do our best to make this answer better.
An error has occurred. We apologize for the inconvenience. Please try again.